Your team is trying to launch richer app experiences. Product wants real-time personalization. Operations wants fewer outages. Customer support wants fewer complaints about lag, dropped sessions, and inconsistent service. Meanwhile, your underlying connectivity stack still behaves like a separate world owned by network specialists, not like a product platform your business can shape.
That gap is where telecommunication software development becomes strategic.
For years, many companies treated telecom software as back-office plumbing. That view no longer holds. The software that manages connectivity, orchestration, provisioning, quality of service, usage data, and network intelligence now directly affects whether your customer-facing products feel fast, reliable, and responsive. It also affects whether your teams can add AI capabilities without turning the system into a cost and governance mess.
That last point matters more than most executives expect. Once AI enters a telecom-adjacent application, the challenge isn't only model selection. It's managing prompts, controlling parameter access, tracking logs across AI services, and understanding cumulative spend before costs drift. Those operational controls are becoming the command center for modern software teams, especially when they need to connect business logic to network-aware experiences.
The New Connected World Runs on Smart Software
A familiar scenario plays out in a lot of boardrooms.
A company invests in a polished mobile app, modern web flows, and better analytics. Then the launch hits production. Video support stutters. Checkout slows during traffic spikes. A new real-time feature works in a demo but struggles under real usage. The root cause often isn't the app alone. It's the software layer underneath connectivity, routing, provisioning, and service management.
That's why telecommunication software development deserves a place in product strategy, not just infrastructure planning.
At a business level, telecommunication software development covers the systems that let providers and digital businesses manage network services, customer interactions, usage, orchestration, and performance through software. That includes the logic behind reliable streaming, secure transactions, low-latency app behavior, connected devices, and intelligent service delivery. When that software is modern, teams move faster. When it isn't, every new feature becomes a negotiation with old architecture.
The market signals are clear. The global telco software market is projected to grow from $30.7 billion in 2024 to $35.1 billion by 2030, and the broader telecommunications industry is set to spend $57 billion on IT in the coming year, according to HG Insights on telecommunications industry spending and telco software growth. That investment isn't about shiny backend tooling. It's about keeping up with complex networks, higher service expectations, and software-driven operations.
Why business leaders should care
If you're in ecommerce, fintech, healthcare, media, or the public sector, telecom software shapes outcomes you already care about:
- Customer experience: Faster, more stable digital interactions reduce friction in moments that matter.
- Feature velocity: Product teams can ship network-aware features without waiting on hardware-heavy change cycles.
- Expansion options: Better software control makes it easier to support distributed users, connected devices, and remote services.
- AI readiness: Intelligent applications need reliable data movement, policy controls, and observability across the stack.
For organizations exploring connected products, the overlap with IoT application development is especially important. The same software discipline that keeps telecom systems resilient also helps connected apps behave predictably at scale.
Smart connectivity isn't a utility purchase anymore. It's part of the user experience.
The shift from network operations to product operations
The strongest teams no longer separate telecom software from digital product delivery. They treat the network layer as programmable, measurable, and responsive to business priorities.
That changes the conversation. Instead of asking, "Can the network support this feature?" teams start asking, "How do we design the software so the feature performs well, scales safely, and creates new value?" That's a much better question.
Understanding Core Telecom Software Architectures
Telecom architecture sounds dense until you translate it into business functions. Most leaders don't need protocol-level depth. They need to know which layers control operations, revenue, flexibility, and speed.
Start with four building blocks.
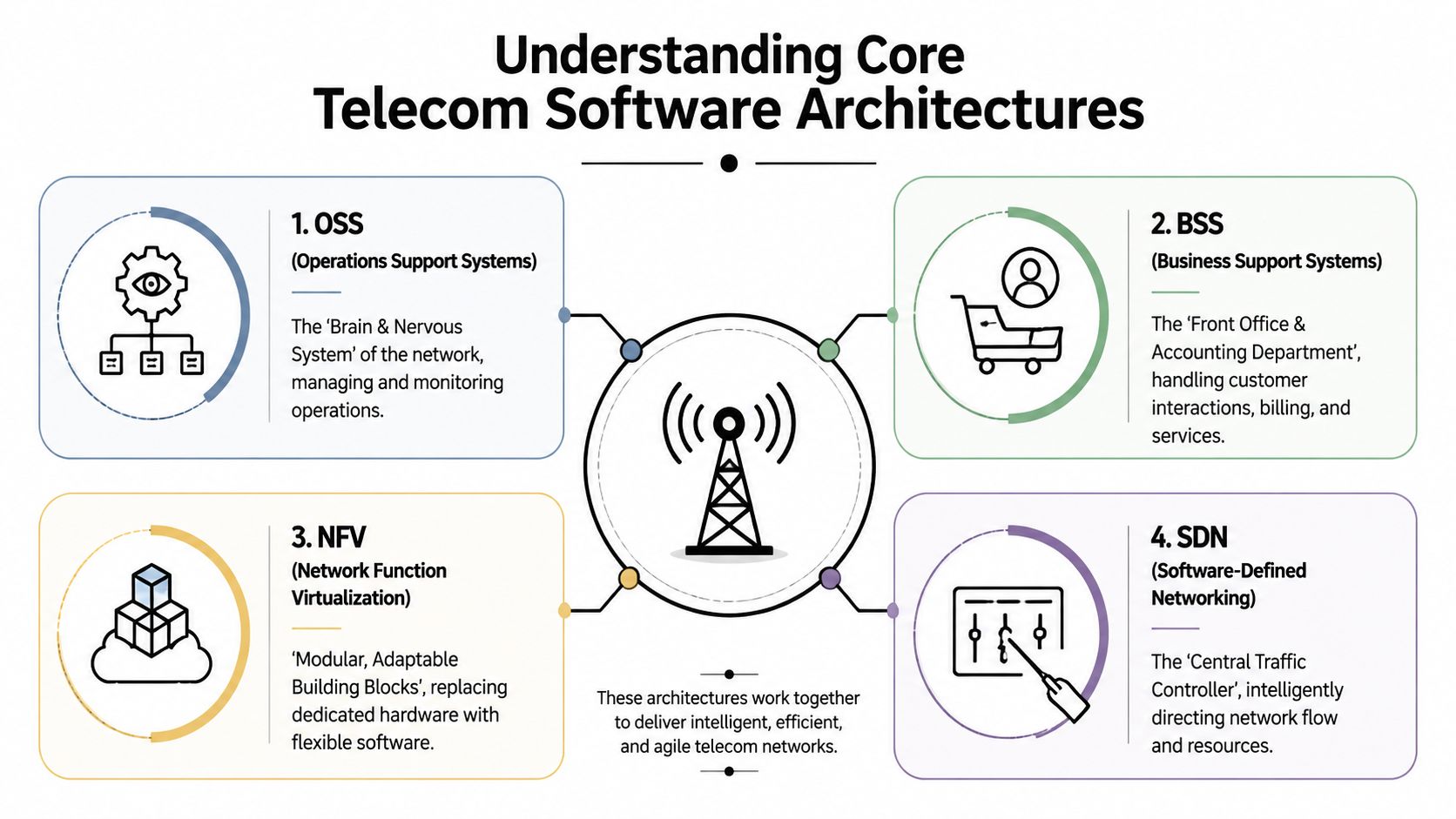
OSS and BSS in plain English
Operations Support Systems (OSS) are the systems that help teams run the network. Think of OSS as the operational brain and nervous system. It handles monitoring, provisioning, fault management, service assurance, and the workflows that keep technical services available.
Business Support Systems (BSS) sit closer to the customer and commercial side. This is the front office and accounting department. BSS handles customer accounts, subscriptions, billing, service catalogs, orders, and often the workflows that connect commercial promises to technical delivery.
A simple way to remember the split:
| Architecture | Best business analogy | What it helps your company do |
|---|---|---|
| OSS | Network operations center | Keep services healthy, observable, and provisioned correctly |
| BSS | Sales ops plus finance | Sell services, bill accurately, and manage customer relationships |
When OSS and BSS are tightly coupled in outdated ways, changes become painful. A billing update can affect provisioning. A network rule change can ripple into customer support workflows. That's why modernization often starts by separating concerns and defining cleaner interfaces.
A lot of the implementation patterns now look more like modern product engineering. Teams use APIs, event-driven workflows, and service boundaries similar to the patterns described in microservices architecture best practices.
SDN and NFV changed the game
If OSS and BSS explain what telecom software manages, Software-Defined Networking (SDN) and Network Function Virtualization (NFV) explain how modern telecom environments stay flexible.
In older environments, capabilities were tied closely to dedicated hardware. That model works until the business needs change quickly. Then every adjustment becomes slow, expensive, and dependent on physical infrastructure decisions.
SDN and NFV shift that model into software. According to GloriumTech's guide to telecommunications software development, these approaches let providers deliver and manage services through software, reduce operational costs, support dynamic service expansion, and provision new services in hours rather than weeks.
What that means in practice
Three business effects show up fast:
- Faster launches: Teams can introduce services without waiting on long hardware-led implementation cycles.
- More predictable costs: Software-defined environments are easier to model, automate, and adjust.
- Better experimentation: Product and platform teams can test new offerings without redesigning the entire foundation.
The most useful telecom architectures don't just keep networks alive. They shorten the distance between business intent and technical execution.
A rigid telecom stack makes every idea feel risky. A programmable stack gives you room to adapt.
Navigating the Major Challenges in Telecom Development
Most telecom software problems aren't caused by one bad technology choice. They come from collision points. Old and new systems collide. Network logic and customer logic collide. Regulatory obligations collide with release speed. That's why telecommunication software development needs a strategy that accounts for constraints from day one.

Legacy integration is usually the first fight
A lot of telecom environments still depend on systems that were stable for years but were never designed for modern product demands. They may hold billing logic, subscriber records, order flows, or operational workflows that nobody wants to destabilize.
The mistake is trying to replace everything at once.
What works better is selective encapsulation. Put APIs around stable legacy capabilities. Move new business logic into services that can evolve independently. Separate urgent product needs from long-cycle core replacement projects. That approach isn't glamorous, but it lowers risk and preserves delivery momentum.
Compliance isn't a side task
Telecom software often lives in regulated environments or supports regulated industries. That means privacy rules, lawful access requirements, data residency concerns, procurement constraints, and local operating policies can all shape architecture decisions.
In emerging markets, those pressures can become even more disruptive. Telecom Business Review on remote-area telecom innovation notes that political instability can delay 30 to 50% of telecom projects in emerging markets, while modern approaches such as SDN can cut compliance cycles by up to 40%.
That matters for business planning. If your expansion model depends on new regions, public-private partnerships, or regulated service delivery, software flexibility becomes part of your risk strategy.
Security and latency pull in different directions
Security teams want tighter controls, more logging, stricter segmentation, and stronger review gates. Product teams want responsiveness. Customers want everything to feel instant. Those goals don't naturally align.
A practical telecom architecture accepts the tension and designs for it:
- Put policy enforcement close to sensitive data
- Use observability to detect unusual behavior early
- Keep high-frequency paths lean
- Avoid routing every decision through a central bottleneck
- Design graceful degradation instead of all-or-nothing failure
Four challenges leaders should watch closely
| Challenge | What goes wrong | Better response |
|---|---|---|
| Legacy coupling | Small changes trigger broad regressions | Wrap, isolate, and migrate in slices |
| Regulatory complexity | Releases stall in approval loops | Build policy-aware workflows into the platform |
| Security exposure | A larger software footprint increases attack surface | Treat identity, access, and logging as architecture |
| Latency sensitivity | Great features fail under real usage conditions | Move critical processing closer to where decisions happen |
Good telecom software teams don't chase elegance first. They reduce operational fragility first.
Leaders who understand these trade-offs make better investment decisions. They stop asking for one-time transformation and start funding repeatable modernization.
A Blueprint for Cloud-Native Modernization
Modernization works best when it's boring in the right places. Repeatable deployments. Predictable environments. Automated tests. Clear service boundaries. That's what gives telecom software the stability to handle fast change.
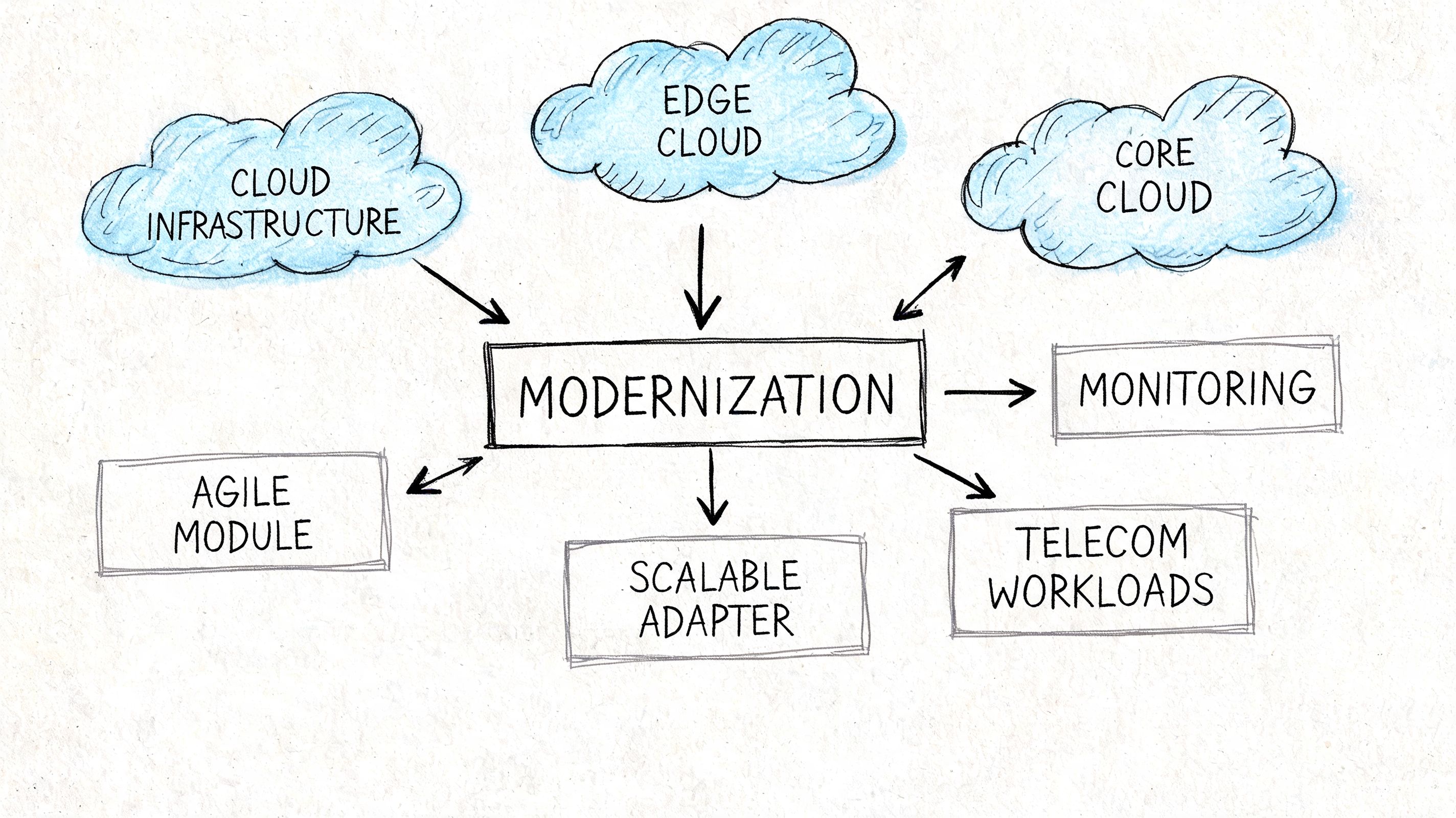
Start with delivery discipline
A lot of organizations talk about cloud-native architecture when what they really need first is release discipline. If deployments are still manual, environment differences are common, and rollback is uncertain, moving to containers alone won't fix much.
A useful modernization pattern usually starts here:
- Standardize environments so development, testing, and production behave more consistently.
- Automate builds and deployments to reduce one-off release rituals.
- Add automated validation for integration, security, and performance risks.
- Instrument everything so teams can see failures, bottlenecks, and usage patterns quickly.
Continuous integration and continuous deployment prove their worth. CI/CD isn't just a DevOps badge. It reduces the business cost of change. Smaller releases are easier to review, easier to reverse, and less likely to break adjacent systems.
For teams planning a broader platform shift, cloud-native architecture guidance provides a helpful lens for thinking beyond lift-and-shift migrations.
Build in modules, not monuments
Monoliths aren't always bad. Some are stable and efficient. But in telecom environments, large tightly coupled systems become expensive when multiple teams need to move at different speeds.
That's why microservices and modular services often work well here. Think of the difference between a box of LEGO bricks and a poured concrete slab. With modular systems, you can replace one capability, scale one component, or isolate one failure domain without rewriting everything.
That doesn't mean every function deserves its own service. Over-fragmentation creates operational overhead. The healthier pattern is to split where business boundaries are real. Billing logic, orchestration workflows, device management, partner integrations, and customer notification systems often evolve on different timelines. Your architecture should reflect that reality.
Testing is not a final phase
Telecom systems fail in combinations. An order enters correctly, but provisioning lags. The service activates, but billing applies the wrong rule. A latency spike appears only during a region-specific workflow.
That means testing must cover more than unit behavior.
Use a layered approach:
- Contract tests to verify service interfaces
- Integration tests for cross-system workflows
- Performance tests for load-sensitive paths
- Security tests for access controls and data handling
- Operational drills for failover, rollback, and incident response
Practical rule: If your team can't rehearse failure, it isn't ready for scale.
Cloud-native modernization isn't one big migration. It's a disciplined shift toward software that can change safely.
Unlocking Intelligence with AI and Machine Learning
AI in telecom gets oversold when people treat it like a futuristic add-on. Its value is much more practical. AI helps teams make faster decisions in environments where manual analysis can't keep up.

Where AI creates operational leverage
The first strong use case is predictive maintenance. Instead of waiting for a visible outage or customer complaint, teams use machine learning to spot patterns that suggest degradation is coming. That lowers disruption and gives operations teams better timing for intervention.
The second is traffic and quality optimization. Telecom environments produce constant streams of signals about performance, congestion, and service conditions. AI models can help route, prioritize, or flag conditions faster than manual review cycles.
The third is customer-facing intelligence. Telecom software increasingly supports products that personalize offers, improve support workflows, or adapt service behavior based on real conditions. For a business leader, that's the bridge between network intelligence and revenue impact.
Why edge intelligence matters
The most overlooked AI lesson in telecom is location. Some decisions can't wait for centralized processing. They need to happen close to the activity itself, especially in distributed or labor-constrained environments.
The Broadband Library discussion of telecom workforce constraints describes how AI-driven automation and edge intelligence can enable agent-driven operations and mini AI factories at remote sites, reducing the need for human intervention by 40 to 60% through automated testing and virtualized network orchestration.
That matters well beyond telecom operators. If you're building software for remote healthcare, distributed retail, field operations, media delivery, or connected financial services, edge-aware AI can keep experiences responsive even when central systems are far away.
Teams need AI skills that are operational, not just theoretical
A common mistake is staffing AI work as a research initiative. Telecom-related AI succeeds when engineers can connect models to live systems, data controls, observability, and user workflows.
A practical upskilling path often includes architecture, MLOps, data handling, and platform security alongside model knowledge. For teams formalizing that capability, this AWS Certified Machine Learning exam prep resource is a useful way to sharpen the fundamentals that show up in production systems.
- Use AI where decision speed matters
- Prefer observable models over black-box magic
- Deploy intelligence near the workflow when latency matters
- Tie model output to business actions, not dashboards alone
AI earns trust in telecom when it prevents friction, not when it produces fancy demos.
The strongest AI programs don't start with ambition. They start with a narrow operational win and expand from there.
Assembling Your High-Performance Development Team
Telecom software projects fail when the team shape is wrong. Not because people are untalented, but because the work spans too many disciplines for a narrow hiring plan. You don't just need network knowledge. You need software people who can work across cloud infrastructure, APIs, observability, security, data pipelines, and user-facing applications.
That mix is getting harder to hire for. According to iTransition's software development statistics roundup, 61% of recent telecom recruits are full-stack developers. The same source notes that 81% of companies view low-code development as strategically vital, with reported gains in process efficiency at 53% and employee productivity at 51%.
What a strong telecom team usually includes
Not every initiative needs every specialty full time, but most successful teams cover these capabilities:
- Platform engineers who understand deployment pipelines, environments, and reliability
- Backend developers who can model telecom logic cleanly and integrate with legacy services
- Frontend or mobile engineers who turn network-aware capabilities into usable customer experiences
- QA specialists who know how to test complex workflows, not just isolated screens
- Security-minded architects who build access control, auditability, and policy compliance into the stack
- AI or data engineers when intelligence, anomaly detection, or personalization is part of the roadmap
A missing role usually shows up as rework. Teams without strong QA tend to discover issues late. Teams without platform depth end up with fragile releases. Teams without product thinking build technically impressive software that users don't enjoy.
Choosing the right staffing model
There isn't one correct team model. The right choice depends on urgency, internal maturity, and how central the software is to your business.
| Team model | Best fit | Trade-off |
|---|---|---|
| In-house build | Long-term core capability | Slower to assemble and harder to rebalance |
| Specialized partner | Complex delivery with limited internal bandwidth | Requires careful partner selection and governance |
| Augmented team | Existing team needs targeted expertise | Coordination can get messy without strong leadership |
In practice, many organizations use a hybrid approach. Keep strategic product ownership internal. Bring in specialized engineering support where architecture, delivery speed, or AI modernization needs exceed your current bench.
Where low-code fits and where it doesn't
Low-code gets dismissed too quickly by technical teams and trusted too blindly by non-technical buyers. The right answer is in the middle.
Low-code works well for internal tools, workflow dashboards, approval flows, administrative interfaces, and early-stage process automation. It doesn't replace careful engineering for high-scale orchestration, performance-sensitive systems, or complex security boundaries.
The useful question isn't, "Should we use low-code?" It's, "Which parts of this platform benefit from speed over custom depth?"
From Plan to Production and Beyond
Shipping telecom software is only the midpoint. The true test starts after launch, when the system has to handle live traffic, changing usage patterns, policy requirements, and feature pressure from the business.
Operations separates resilient platforms from impressive prototypes.
What production success looks like
Healthy telecom software operations usually have four qualities.
First, teams can see what's happening in real time. They monitor service health, latency-sensitive paths, integration behavior, and suspicious events without waiting for support tickets to reveal problems.
Second, the platform can scale without drama. Autoscaling, queue management, and workload isolation help the system absorb spikes without forcing engineers into midnight interventions.
Third, teams maintain governance without paralysis. They know what changed, who changed it, what it cost, and how to reverse it if needed.
Fourth, the software remains adaptable. New AI features, customer workflows, or service policies can enter the system without destabilizing the core.
AI operations need their own control layer
Many modernization programs hit a second wave of complexity. The application may be cloud-native. The telecom workflows may be modular. However, once AI enters the product, operational discipline has to expand again.
Teams need a way to manage prompt versions so behavior doesn't undergo unmanaged changes. They need a parameter layer that controls how AI interacts with internal databases and system context. They need unified logging across integrated AI services so debugging isn't fragmented. And they need cost visibility that shows cumulative spend before experimentation becomes a budgeting problem.
Without those controls, AI-enhanced telecom software becomes hard to govern. You may still ship features, but you'll struggle to maintain consistency, auditability, and financial discipline over time.
A durable operating model
A practical operating model for telecommunication software development includes:
- Release management that tracks software and AI behavior together
- Observability across apps, integrations, and intelligent workflows
- Policy-aware access controls around data exposure and system actions
- Cost review routines for infrastructure and AI usage, not just cloud runtime
- Continuous tuning based on production feedback, not assumptions from prelaunch testing
Production readiness in telecom isn't about preventing all change. It's about making change controllable.
If you're modernizing a platform that now depends on AI for support, personalization, classification, or operational decisioning, that control layer becomes part of the product itself.
If your team is modernizing legacy systems, building AI-enabled applications, or trying to make telecommunication software development support real business outcomes, Wonderment Apps can help. Their team works across web, mobile, AI modernization, and scalable product engineering, and they’ve built an administrative prompt management system with a versioned prompt vault, parameter manager for internal database access, unified AI logging, and cost tracking to help teams ship smarter software with tighter operational control. If you want to see how that toolkit fits into your architecture, book a demo with Wonderment Apps.